Health Sector Cybersecurity Framework Implementation
Health Care and Public Health Sector Cybersecurity Framework Implementation Guide
While the generic cybersecurity framework implementation approach outlined in Appendix C – NIST Cybersecurity Framework Basics works well for organizations that design or specify their own controls, it does not work as well (i.e., most efficiently) for those organizations that leverage external control frameworks such as those provided by the NIST Cybersecurity Framework's Informative References[34]. Fortunately, this generic implementation approach can be modified to accommodate a controlled framework-based approach to risk analysis and control specification.
The primary reason for the modification is that, for those organizations that already leverage or intend to leverage one or more Informative References, Target Profiles are easily obtained once organizations are able to scope their organization and systems and then tailor the Informative Reference(s) to address any unique threats/risks. There is no need to develop a Current Profile beforehand. Placement of the Current and Target Profiles can subsequently be reversed, although some basic information about the state of the organization's cybersecurity program will necessarily be ascertained before the Target Profile is complete.
Implementation Process
The Cybersecurity Framework can be used to compare an organization's current cybersecurity activities with those outlined in the Framework Core. Through the creation of a Current Profile, organizations can examine the extent to which they are achieving the outcomes described in the Core Categories and Subcategories, aligned with the five high-level Functions: Identify, Protect, Detect, Respond, and Recover. An organization may find that it is already achieving the desired outcomes, thus managing cybersecurity commensurate with the known risk. Alternatively, an organization may determine that it has opportunities to (or needs to) improve. The organization can use that information to develop an action plan to strengthen existing cybersecurity practices and reduce cybersecurity risk. An organization may also find that it is overinvesting to achieve certain outcomes and use this information to reprioritize resources. Figure 2 illustrates how an organization could use the Framework to create a new cybersecurity program or improve an existing program. These steps should be repeated as necessary to continuously improve cybersecurity.[35]
Figure 2. Health Care Implementation Process 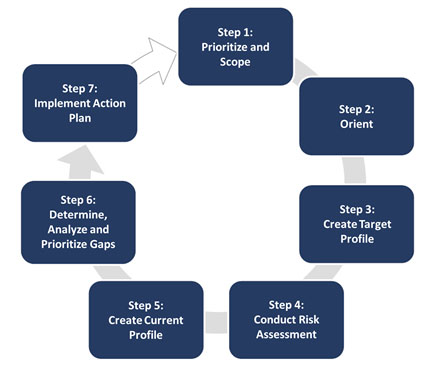
HPH Sector organizations leveraging Informative References[36] as the basis for their cybersecurity programs can use the following seven-step process for implementation depicted in Figure 2, which slightly modifies the general approach outlined in the NIST Cybersecurity Framework.[37]
As with the generic process, it is recommended that implementation include a plan to communicate progress to appropriate stakeholders, such as senior management, as part of its risk management program. In addition, each step of the process should provide feedback and validation to previous steps.
Each step is now discussed in more detail, first introduced by Table 1 describing the step's inputs, activities, and outputs followed by additional explanation.[38] A table of the inputs, activities, and outputs for all seven steps is also included in Appendix G – Summary of Health Care Implementation Activities.
The risk management process should begin with a strategy addressing how to frame, assess, respond to, and monitor risk. For health care organizations, leveraging one or more Informative References is a central component of that strategy as it forms the basis of their risk analysis, informs the organization on the minimum level of due care and due diligence required to meet its multiple compliance obligations, provides for the adequate protection of individually identifiable health information and other sensitive information, and provides a comprehensive and rigorous methodology for control assessment, scoring, and reporting. The organization's risk strategy is also used to inform investment and operational decisions for improving or otherwise remediating gaps in their cybersecurity and information protection program.
In this step, the organization decides how and where it wants to apply the Informative References (its usage scope) - whether in a subset of its operations, in multiple subsets of its operations, or for the entire organization. This decision should be based on risk management considerations, organizational and critical infrastructure objectives, priorities,[39] availability of resources, and other internal and external factors. Current threat and vulnerability information from a nationally recognized Information Sharing Analysis Organization (ISAO) may also help inform scoping decisions. All types of threats and vulnerabilities, including cyber-physical threats, that are relevant to the organization should be considered.
An organization that is using one or more Informative References for the first time might want to apply it to a small subset of operations to gain familiarity and experience with it. After this activity, the organization can consider applying the Informative References to a broader subset of operations or to additional parts of the organization as appropriate by applying the following elements of a risk analysis:
-
Conduct a complete inventory of where electronic protected health information (ePHI) is created, received, maintained, or transmitted (if not already performed)
-
Perform a Business Impact Analysis (BIA) on all systems that create, receive, maintain, or transmit ePHI (criticality)
-
Categorize & evaluate these systems based on sensitivity and criticality
The organization identifies the systems, assets, compliance and best practice requirements, and any additional cybersecurity and risk management approaches that are in scope. This includes standards and practices the organization already uses and could include additional standards and practices that the organization believes would help achieve its critical infrastructure and business objectives for cybersecurity risk management. The organization's risk management program may already have identified and documented much of this information, or the program can help identify individual outputs. A good general rule is to initially focus on critical systems and assets and then expand the focus to less critical systems and assets as resources permit.
| Inputs | Activities | Outputs |
|---|---|---|
|
|
|
The NIST Risk Management Framework (RMF) shown in Figure 3 below provides organizations an overarching risk management process that integrates security, privacy, and cyber supply chain risk[40] management activities into the system development life cycle. The risk-based approach to control selection and specification provided in the first three steps of the seven-step process - shown in Figure 4 in Step 4 - considers effectiveness, efficiency, and constraints due to applicable laws, regulations, policies, standards, contractual, and similar obligations. This RMF approach can be applied to new and legacy systems, any type of system or technology (e.g., IoT, control systems), and within any type of organization regardless of size or sector.[41]
Figure 3. NIST Risk Management Framework 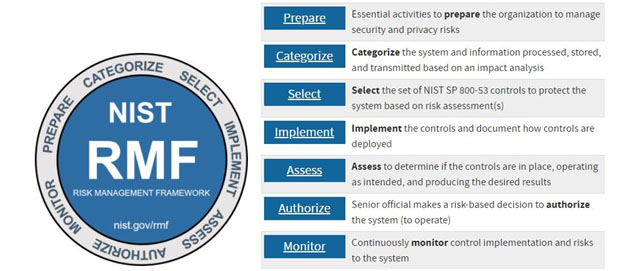
The organization considers the cyber threats and subsequent risk to its operations as determined during the first two steps to create a tailored overlay of its selected Informative Reference(s) to account for any unique threats/risks (as compared to other, similar organizations that are the target(s) of the Informative Reference(s)). The Target Profile should include these practices as well.
However, information protection cannot be a "one size fits all" approach. For example, organizations, more often as not, have different information systems (or different implementations of similar systems), different business and compliance requirements, different cultures, and different risk appetites.[42]
For whatever reason an organization cannot implement a control specified by its selected Informative Reference(s), one or more compensating controls should be selected to address the risks posed by the threats the originally specified control was meant to address. (Note these compensating controls may already exist within the organization and should be leveraged appropriately.)
Organizations should be able to demonstrate the validity of a compensating control by way of a legitimate risk analysis that shows the control has the same level of rigor and addresses a similar type and level of risk as the original. Additionally, the compensating control must be something other than what may be required by other, existing controls specified in the tailored overlay of its selected Informative Reference(s).
The organization should determine the evaluation approach it will use to identify its current cybersecurity and risk management posture. Organizations can use any of several evaluation methods to identify their current cybersecurity posture and create a Current Profile. These include self-evaluations, where an organization may leverage its own resources and expertise; facilitated approaches, where the evaluation is assisted by a third party; or completely independent evaluations, such as those used to support certification or accreditation against the Informative Reference(s) or an American Institute of Certified Public Accountants (AICPA) [43] Service Organization Control 2 (SOC 2) [44] that uses the organization's selected Informative Reference(s) as the basis for assessment. [45]
The organization should also determine its goals for the Target Tier from the NIST Cybersecurity Framework and identify the equivalent levels of control maturity required to achieve those goals. This will generally involve mapping relevant controls from the organization's cybersecurity program to the topical areas (characteristics) addressed by the Tiers (i.e., Risk Management Process, Integrated Risk Management Program, and External Participation) and then evaluating these areas (characteristics) for their respective Tier (i.e., 1 – Partial, 2 – Risk Informed, 3 – Repeatable, and 4 – Adaptive):
-
Select an appropriate framework baseline set of controls
-
Apply an overlay based on a targeted assessment of threats unique to the organization
Organizations perform cybersecurity risk assessments to identify and evaluate cybersecurity risks and determine which are outside of current tolerances. The outputs of cybersecurity risk assessment activities assist the organization in developing its Current Profile and Implementation Tier based on control maturity (see Step 5). For organizations that have a risk management program in place, this activity will be part of regular business practice, and necessary records and information to make this determination may already exist. For example, many organizations perform regular evaluations of their programs through internal audits or other activities, which may describe the controls as implemented within the defined scope of the risk assessment.
Note, this step includes the following element of a risk analysis as modified to accommodate the use of one or more NIST Cybersecurity Framework Core Informative References: Evaluate residual risk. [46]
A Current Profile is created from the evaluation of the organization's cybersecurity and risk management practices against the Target Profile created in Step 4.
The organization evaluates its Current Profile and Implementation Tier against its Target Profile and Target Implementation Tier and identifies any gaps. When mapping back to the NIST Cybersecurity Framework, a gap exists when there is a desired Category or Subcategory outcome in the Target Profile or program characteristic in the Target Implementation Tier that is not currently achieved by the organization's existing cybersecurity and risk management approach, and when current practices do not achieve the outcome to the degree of satisfaction required by the organization's risk management strategy.
After controls are specified by an organization to ensure risk is controlled to a level formally deemed acceptable by executive leadership, the most common way of dealing with (i.e., treating) deficiencies observed with the implementation and management of those controls is to remediate them. This reduces risk to an acceptable level, a process referred to as mitigation.
Cybersecurity Risk Management
Although ostensibly intended for U.S. Federal Agencies, NIST provides excellent guidance on how to manage cybersecurity risk that is also applicable to private sector organizations. For example, NIST SP 800-39 provides guidance for an integrated, organization-wide program for managing information security risk to organizational operations (i.e., mission, functions, image, and reputation), organizational assets, individuals, and other organizations resulting from the operation and use of information systems. It also provides a structured, yet flexible approach for managing information security risk that is intentionally broad-based, with the specific details of assessing, responding to, and monitoring risk on an ongoing basis provided by other supporting NIST security standards and guidelines.[47]
Cybersecurity in Enterprise Risk Management (ERM)
Cybersecurity risk is often managed independently of other types of business risk due to generally dissimilar oversight and reporting requirements;[48] however, it is generally in the best interest of an organization to manage all business risk holistically as part of a broader ERM program, which will help 'min-max' its return on investment and reduce strategic, operations, reporting, and compliance risk, as shown in Figure 4.[49]
Figure 4. Relating Cybersecurity Risk to Other Forms of Business Risk 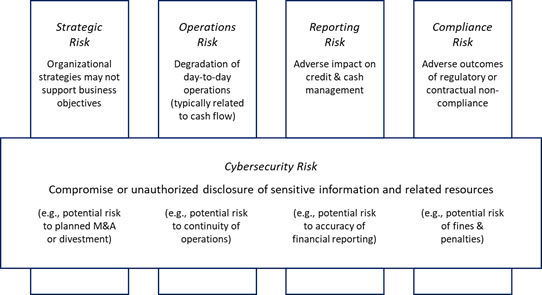
Subsequently, organizations should ensure they identify, evaluate, and communicate cybersecurity risk in the same way other business risks are communicated to senior decision makers. In addition to developing a specific plan of action to address control gaps, organizations should also track associated risks in one or more cybersecurity risk registers, which in turn should be integrated with other risk registers (e.g., financial, and regulatory compliance) to create an Enterprise Risk Register (ERR).[50] The ERR should then be used to create an enterprise risk profile to help senior decision-makers determine which risks should be addressed, to whom responsibilities should be assigned, and how resources should be allocated.[51] Note the risk profile should be updated whenever the underlying cybersecurity risk registers are updated, e.g., after a risk assessment or when risk responses are completed.[52]
Scoring and Reporting
By leveraging an implementation maturity model such as the one presented by NIST[53] and applying an ordinal scoring model, it's possible to evaluate and score how well an organization achieves the outcomes specified by the NIST Cybersecurity Framework's Core Subcategories based on the aggregate of the controls assigned.[54]
The NIST model uses five levels of implementation maturity (ML), as shown in Table 7.
We present two types of maturity scales based on a 'traditional' bell-shaped model and a left-skewed bell-shaped 'academic' model based on similar risk reporting models. Although the traditional model is best used for communicating compliance to external stakeholders, the academic model provides a very intuitive approach to understanding compliance when presented as grades, reminiscent of the model used by the federal government to report security status of federal agencies.
Table 8 on the following page provides the intervals for both models:
A manually constructed scorecard based on the NIST Cybersecurity Framework Functions and Categories using a traditional scoring model is provided in Figure 5 on the next page. In this example, specific controls mapped to each of the NIST Cybersecurity Framework's Core Subcategories would have been individually evaluated and scored (potentially using the approach just described), and those scores would be aggregated and averaged according to how they mapped to the Subcategories. The Subcategory scores would then be aggregated and averaged for their 'parent' Categories and reflected as shown in Figure 5. Category scores would be similarly aggregated, averaged, and displayed for their respective Functions.
Figure 5. Example NIST Cybersecurity Framework Scorecard 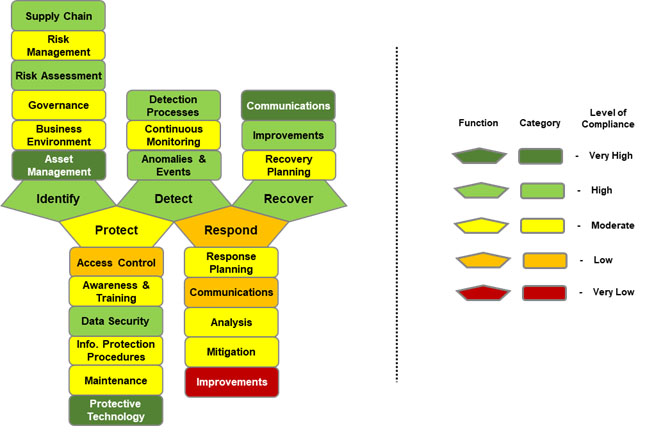
Corrective Action Plans
Deficiencies or 'gaps' in a control's implementation should be corrected immediately or a Corrective Action Plan (CAP) should be developed that outlines the activities and technology required to remediate the gap.
The organization executes the CAP and tracks its progress over time, ensuring that gaps are closed, and risks are monitored. CAPs can be used as the overarching document to track all capital (projects) and operational work performed by the organization to address gaps in its Target Profile.
A complete CAP should include, at a minimum, a control gap identifier, description of the control gap, control mapping, point of contact, resources required (dollars, time, and/or personnel), scheduled completion date, corrective actions, how the weakness was identified (assessment, assessor name, date), date identified, and current status.
Note, this step includes the following element of a risk analysis as modified to accommodate use of a control framework: Implement corrective actions and monitor the threat environment.
Implementation Conclusion
This implementation approach can help organizations leverage Informative References to establish a strong cybersecurity program or validate the effectiveness of an existing program. It enables organizations to map their existing program to the NIST Cybersecurity Framework, identify improvements, and communicate results. It can incorporate and align with processes and tools the organization is already using or plans to use.
The process is intended to be continuous, repeated according to organization-defined criteria (such as a specific period or a specific type of event) to address the evolving risk environment. Implementation of this process should include a plan to communicate progress to appropriate stakeholders, such as senior management, as part of its overall risk management program. In addition, each step of the process should provide feedback and validation to previous steps. Validation and feedback provide a mechanism for process improvement and can increase the overall effectiveness and efficiency of the process. Comprehensive and well-structured feedback and communication plans are a critical part of any cybersecurity risk management approach.
34 NIST (2022a). National Online Informative References Program, Informative Reference Catalog.
35 NIST (2022a). NIST (2018, Aug 16), p. 14.
36 NIST (Updated 2021, Dec 8). Informative References: What are they, and how are they used
37 NIST (2018, Apr 16), pp. 13-15.
38 The tables describing the activities in the 7-step implementation process are derived from DOE (2015).
39 HHS (2016, May).
40 For more information on aligning an enterprise supply chain cyber security program to the NIST CSF, see HSCC CWG (2020, Sep). Health Industry Cybersecurity Supply Chain Risk Management Guide Version 2.0 (HIC-SCRiM v2.0).
41 NIST (2022b). NIST Risk Management Framework RMF.
42 For more information on risk appetite, see Stine, K., Quinn, Stephen, Witte, G., and Gardner, R. (2020, Oct).
43 AICPA (2020a). AICPA.
44 AICPA (2020b). SOC 2® - SOC for Service Organizations: Trust Services Criteria.
45 AICPA (2020c). SOC 2 Examination That Addresses Additional Subject Matters and Additional Criteria.
46 There are multiple approaches to evaluating risk:
-
For an example of a qualitative approach, see Alberts, C. and Dorofee, A. (2002). Managing Information Security Risks: The OCTAVE Approach. Boston: Addison-Wesley Professional.
-
For examples of a semi- or quasi-quantitative approach, see:
-
Joint Task Force Transformation Initiative (2012, Sep). Guide for Conducting Risk Assessments (NIST SP 800-30 Revision 1). Gaithersburg, MD: NIST.
-
Cline, B. (2017). Risk Analysis Gu ide for HITRUST Organizations and Assessors.
-
-
For an example of a quantitative approach, see Freund, J. and Jones, J. (2015). Measuring and Managing Information Risk: A FAIR Approach. Oxford: Elsevier, Inc.
47 JTF TI (2011, Mar). Managing Information Security Risk: Organization, Mission, and Information System View (NIST SP 800-39). Gaithersburg, MD: NIST.
48 Stine, K., Quinn, S., Witte, G., and Gardner, R. (2020, Oct), p. 2.
50 Quinn, S., Ivy, N., Barrett, M., Feldman, L. Witte, G., and Gardner, R. (2021, Nov). Identifying and Estimating Cybersecurity Risk for Enterprise Risk Manageme nt (NISTIR 8286A).
51 Stine, K., Quinn, Stephen, Witte, G., and Gardner, R. (2020, Oct), pp. 40-42.
52 Ibid., p. 17.
53 Bowen, P. and Kissel, R. (2007). Program Review for Information Security Management Assistance (PRISMA), NISTIR 7358, Wash., DC: NIST.
54 It's important to note that 'achievement' is measured in terms of the control requirements the organization states it needs to achieve the outcomes specified by the Framework's Core Subcategories, and those requirements should be based on an appropriate risk analysis.

